IBM, Lenovo, HPE and Huawei Servers Rank as Most Secure Platforms in ITIC Survey
IBM, Lenovo, Huawei and Hewlett-Packard enterprise servers ranked as the most secure platforms in an ITIC survey—experiencing the fewest number of successful data breaches
For the third straight year, corporate enterprises ranked mission critical IBM, Lenovo, Huawei and Hewlett-Packard enterprise servers as the most secure platforms which experienced the fewest number of successful data breaches and are the quickest to detect attempted breaches.
IBM, Lenovo, Huawei, HPE and Cisco maintained their top positions as the most secure server platforms despite a significant 84% spike in security hacks over the last two years, according to the ITIC 2022 Global Server Hardware Security survey. The independent web-based study compared the effectiveness of the inherent security capabilities of 15 different server platforms and polled 1,300 businesses worldwide across 28 different vertical market sectors from November 2021 through mid-March 2022.
The survey found that security incidents like ransomware, email phishing scams and targeted data breaches were especially prevalent and commonplace. A 76% majority of ITIC respondent firms cited security as the number one issue and biggest threat to server hardware and server operating system reliability.
Mission critical systems led by the IBM Z and IBM LinuxONE III; the IBM POWER9 and Power10; the Lenovo ThinkSystem; Huawei KunLun; HPE Superdome Flex; and Cisco UCS servers (in that order) delivered the most solid, across-the-board security capabilities. More specifically, these servers experienced:
- The fewest number of successful security hacks/data breaches
- The least amount of overall unplanned server downtime as the result of a security incident
- The fastest mean time to detection (MTTD) from the onset of the attempted attack until the company isolated and shut it down
- The fastest overall mean time to remediation (MTTR) to restore servers, applications and networks to full operation
- The least amount of lost, stolen, destroyed, damaged or changed data as a direct consequence of a data breach
- The least amount of monetary losses due to a successful security hack
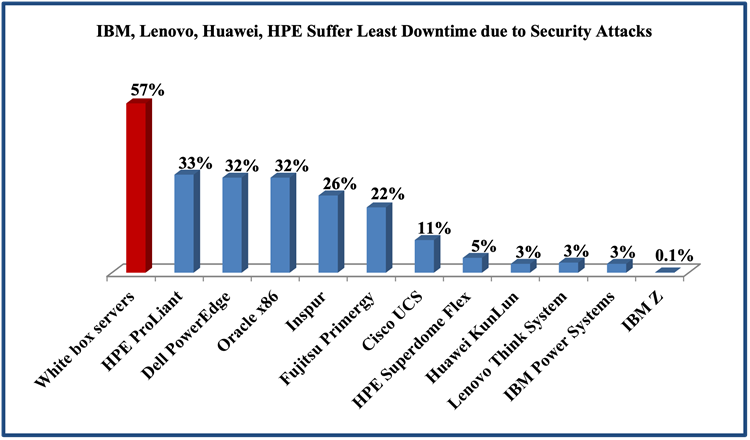
As Figure 1 illustrates, IBM’s z14 and z15 distributions again exhibited the most solid security, outperforming all other competitors. Only a minuscule 0.1% of IBM Z high-end server enterprise customers reported a successful data breach that resulted in tangible downtime or compromised or stolen data.
Among other mainstream hardware platforms, just 3% of IBM POWER9 and Power10, Lenovo ThinkSystem and Huawei KunLun users reported their systems were successfully hacked, while 5% HPE Superdome Flex server customers reported successful security breaches resulting in downtime. Additionally, the most secure IBM, Lenovo, Huawei, HPE and Cisco distributions experienced the least amount of lost, stolen, destroyed, damaged, changed or compromised data.
Source: ITIC 2022 Global Server Hardware Security Survey
Just over one in 10, or 11%, of Cisco UCS server customers reported a data breach. The relative robustness of Cisco’s hardware is noteworthy: Many UCS servers are deployed in remote locations and at the network edge. These locales often lack onsite security and IT administrators even though they are frequently the first (and repeated) point of attack.
Unbranded white box servers again proved most porous; 57% of respondents experienced security hacks. Many of the firms that deploy inexpensive, unbranded servers often run unlicensed or pirated software which is more vulnerable to breaches.
Early Detection Is Key to Thwarting Security Breaches, Minimizing Damage
Cybersecurity threats are the biggest concern for companies globally in 2022, according to 44% of security respondents to the 11th Annual Allianz Risk Barometer survey. The survey, conducted by Allianz Global Corporate & Specialty (AGCS), a financial services firm based in Munich, Germany, polled 2,650 security experts in 89 countries.
Figure 2 shows that once again, the IBM Z, IBM Power Systems, Lenovo ThinkSystem, Huawei KunLun and Fusion Servers, HPE Superdome and Cisco UCS Servers (in that order) excelled in thwarting hacks. These servers had the best MTTD percentages among all server platforms and consequently the top five server distributions, and experienced the fewest number of actual data breaches.

Source: ITIC 2022 Global Server Hardware Security Survey
An overwhelming 96% of IBM Z and IBM LinuxONE III survey respondents indicated the inherent pervasive encryption features in the platform were able to detect an attempted security breach “immediately or within the first one to 10 minutes” of the attack, isolate it and shut it down. They were followed in order by the IBM Power Systems, Lenovo ThinkSystem and Huawei KunLun distributions; 93% of each of these platform users said the security capabilities within these server distributions enabled their security and IT administrators to recognize and repel a security breach within the first 10 minutes. The faster the critical core infrastructure servers, OSes and mission-critical applications can repel a hack, the better the chances the business will experience little or no downtime or fall victim to stolen, changed, damage, or compromised data and IP theft.
The fact that over nine in 10 IBM, Lenovo, Huawei and HPE enterprises detected and repelled attempted data breaches stands in stark contrast to the industry average MTTD statistics. Overall, 52% of respondents across all 15 server hardware platforms polled, were “unsure or unable to determine how long it took their firms to identify and shut down security hacks.”
The sharp increase in cyberattacks makes early detection imperative, security experts say.
“Early detection and any detection at all is crucial, is important,” says Andrew Baker, president and CTO of Brainwave Consulting in Gassaway, West Virginia, a security consultancy specializing in mid-sized enterprises. He notes that in 2022 it’s tougher for organizations to thwart attacks compared to five years ago.
“There are more attackers; they are more skilled; they are more connected – via networks, cloud, virtualization and IoT ecosystems and the cybercrooks have a vast amount of resources at their disposal,” Baker says. “Organizations need strong security practices in combination with servers that can provide embedded security capabilities and defenses to move beyond prevention and focus on detection and response,” he adds.
According to Baker, “The quicker companies are alerted to attempted data breaches [on their servers and mission critical applications], the greater the likelihood they can isolate and shut down the attack before the hackers can do damage and access sensitive data.”
Data Breaches Are Big Business
Robust server security that provides top notch MTTD and MTTR saves money and mitigates risk.
ITIC’s latest 2022 survey results indicated that a single hour of server downtime now costs 91% of mid-size and large enterprises upwards of $300,000 or more. And 44% of respondents said their hourly outage costs exceed $1 million to over $5 million.
Organizations like banks, school districts and municipalities that suffer a protracted outage of hours, days or longer, leaving them unable to access mission-critical data, will almost certainly incur many millions in damages and put the business at risk of litigation and even closure.
ITIC’s latest cyberstatistics are bolstered by survey results from global security agencies and U.S. Federal government agencies which have issued multiple cybersecurity risk alerts since the beginning of 2020. The Federal Bureau of Investigation (FBI); the Department of Homeland Security’s Cybersecurity and Infrastructure Security Agency (CISA) as well as other government agencies like the Securities and Exchange Commission’s (SEC) Office of Compliance Inspections and Examinations (OCIE) have issued dozens of cyberalerts over the last 24 months.
The FBI’s 2021 Internet Crime Report, released in March 2022, found that cybercrimes cost Americans companies and consumers $6.9 billion last year. This is more than triple the $2 billion in losses reported in 2020. According to the FBI, it received 847,376 complaints of suspected internet crime; this is a 7% rise compared to 2020. The FBI 2021 Internet Crime Report said the top three cyber crimes reported by victims in 2021 were: “phishing scams, non-payment/non-delivery scams, and personal data breach.”
In order to fully assess the costs and damages associated with security hacks and data breaches corporations will also have to perform a forensic type of analysis to track the source of the data breach. They must also identify the severity, duration and type of hack. This deep analysis requires inherent server-based data analytics, AI working in concert with embedded security functions. These are all areas in which the IBM Z, IBM Power, Lenovo ThinkSystem, Huawei KunLun, HPE Superdome Flex and Cisco UCS servers excel as a result of years long investment in the underlying server-based security features.
No one and nothing is immune. Inherent, robust server infrastructure security is imperative.