SecureCare: IBM i Security and Compliance Expertise at Your Side

Cybersecurity continues to dominate IBM i planning conversations, with 64% of this year’s IBM i Marketplace Survey respondents citing it as a top IT concern. Yet many organizations are simultaneously grappling with:
- A shortage of IBM i expertise
- Overextended teams
- Difficultly building a clear security and compliance plan
When your team is already stretched thin and specialized skills are hard to find, knowing where to begin can feel overwhelming.
Partner with IBM i Security and Compliance Experts
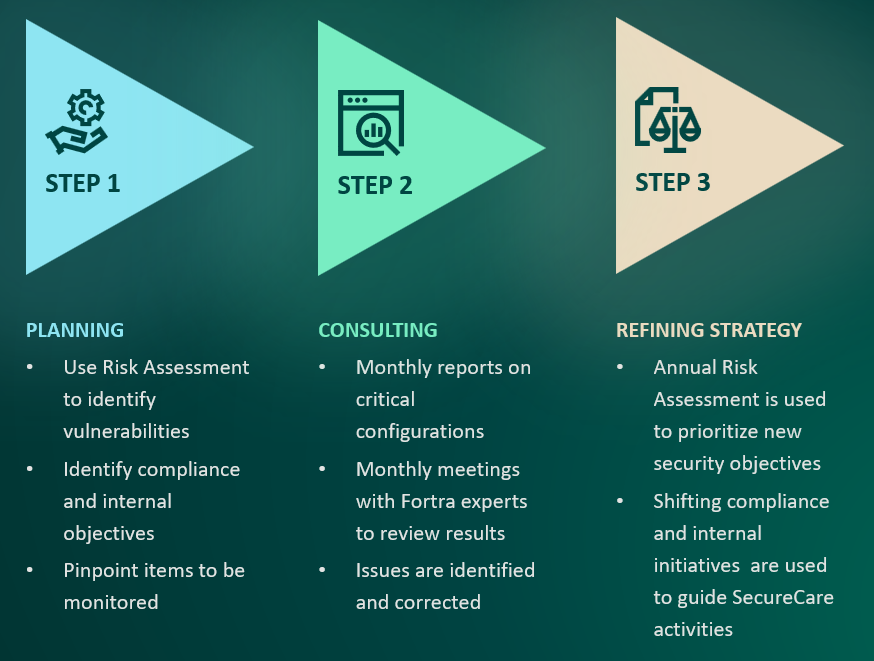
Fortra’s SecureCare for IBM i is a service that offers a simple and efficient way to identify security vulnerabilities on your system. With multiple IBM Champions and CISSP, CISA, and PCIP-certified experts looking out for your organization’s best interests, you can stop worrying that key risks will be overlooked or that the next compliance audit will result in fines or penalties.
With SecureCare for IBM i:
- Fortra’s experts will conduct a full security audit. They’ll use the results to help you identify key misconfigurations and prioritize action items. We’ll assess your system’s security vulnerabilities and provide you with a detailed report and recommendations.
- Key security configurations are monitored and reports from your systems are scheduled and securely emailed to Fortra’s team of IBM i security experts for analysis.
- If issues are discovered, they are highlighted in the monthly report and Fortra’s team provides guidance on how to remediate them.
- You cantake the pressure off your system administration staff and facilitate regular security attention.
With industry-recognized specialists proactively monitoring your environment, SecureCare for IBM i gives you confidence that your system is protected, your risks are addressed, and your compliance obligations are supported.
Don’t Let Risky Misconfigurations Slip Through the Cracks
A misconfigured system is a vulnerable system, increasing the risk of a data breach. While the appropriate security controls may have been in place at one time, misconfiguration occurs gradually. Settings are changed one by one, without consideration for your security policy or level of risk tolerance. Guarding against this problem is as simple as ongoing monitoring of your system. But the people doing the monitoring need to know what they’re looking for. With SecureCare, security experts monitor your system configuration, so that changes to settings can be identified in a timely manner. This gives you the information necessary to make changes that elevate your security posture and minimize risks.
Some monitoring activities our experts conduct include:
- Discovering and ensuring inactive profiles are disabled
- Identifying new profiles with special authorities
- Detecting changes to system values
- Monitoring the security of a critical file (e.g., a file containing confidential or private information)
- Monitoring authority changes to authorization lists
- Discovering profiles with default passwords
- Discovering new programs that adopt authority
- Identifying new file shares
- Authority failures to a set of objects or to a specific object
Facilitate Audit Readiness and Alignment with System
Administrators
Preparing audit reports can be grueling work. Without the right tools or know-how, generating the reports auditors need can take hours or even entire days. SecureCare makes compliance audits painless. Industry-leading security experts monitor your security settings and prepare detailed reports, helping you bridge the gap between systems administrators and auditors. Beyond regular monitoring and reporting, SecureCare’s robust security use cases provide versatility in addressing specific compliance frameworks like PCI-DSS, SOX, HIPAA, CIS, GDPR, NIST, and ISO 27001.
The following are real examples of PCI-DSS requirements that SecureCare helps fulfill:
- Requirement #3: Protect Stored Account Data: SecureCare helps your team attain least privilege status so that only those with a need-to-know will have access to sensitive information.
- Requirement #4: Protect Cardholder Data with Strong Cryptography During Transmission: The SecureCare team has experience configuring TLS 1.2 and TLS 1.3 for all IBM native communications like FTP, Telnet, DDM, and others to help your team ensure that no sensitive data is flowing unencrypted across your network.
- Requirement #8: Identify Users and Authenticate Access to System Components: The SecureCare team can help you identify any profiles that may pose a risk to your system and work with you to establish a governance plan for making sure these risks are mitigated going forward. Read Fortra’s guide for the complete breakdown on how SecureCare helps organizations achieve PCI-DSS compliance.
Who Can Benefit from SecureCare?
Any organization that relies on IBM i and wants greater confidence that misconfigurations, risky authorities, or overlooked vulnerabilities won’t slip through the cracks can benefit from the added assurance of SecureCare’s expert, ongoing security monitoring. SecureCare is a particularly good fit for IBM i shops that are juggling staffing shortages, growing compliance demands, or limited in-house IBM i security expertise.
Want to Get Started with SecureCare for IBM i?
Find out if SecureCare is right for you. Contact Fortra to get more details and discuss your organization’s needs.